Networking Basics: Applications of Network Devices
I wrote this article to help people understand basic network devices. It would be useful to individuals who want to learn a few more details and for anyone studying to take a networking exam such as Network+. I try to focus on the application of these network devices and what they are used for.
Network Devices
There are a lot of different kinds of network devices being made right now. They used to be much simpler as well. Now, we see hybrid devices as well as dedicated network devices. They mix and match functions as needed. There is almost always a device for your needs. The trouble is finding the right one for your network.
I am hoping this article will clear up some of the mystery about the network devices and what they do. If you know the information in my guide then you should be able to make a smart decision when you are ready to make a purchase.
Networking Hub
Hubs are examples of simple network devices. For the most part, it is not smart or managed. It is simple a pass-through for data packets. It does provide a means of connecting parts of your network together. This is what it is usually used for. A hub can not send and receive information at the same time like a nice switch can.
In today's networked world, you do not often see plain hubs anymore. A switch or router often does the job of a hub plus its own tasks. Routers have really taken over the roles of older network equipment. It is common to see routers that have firewalls, switching capabilities, and other functions all within a single box.
Where hubs are useful is connecting parts of a network together that do not need any specialized management. There are a few places where this applies in businesses. Most of the time though hubs work well in homes to extend a network for added network devices. Its main advantage is that it will be cheaper than a switch or a router.
Unmanaged Switches
A switch is a better device than a hub. While it will be more expensive it also does a lot more and will make your network a little faster. Multiple switches are often used at a single location. The number of switches you have is determined by how large an environment you have.
Large networks will have many network devices like switches and access points for example. Switches can be a 4-port or a 48-port variety. They allow different parts of your network to talk to each other.
A switch can be a simple unmanaged type. This means it will work after hooking it up. Nothing to configure. This is often home networking equipment though and has far fewer features of good managed switches.
Managed Switches
Managed switches are very nice network devices. They are often faster and can be configured o work with your network. A big advantage of a managed switch is that they can monitor traffic on your network. There status can be indicated simple by looking at them using there software. You can also remote into a switch and perform any necessary tasks that you need.
Unlike a hub, switches can inspect network traffic before it sends it on. Packet inspection is what makes these devices really valuable. They only send traffic forward that meets requirements. This makes your network quicker and more reliable.
Most regular switches operate at the second level of the OSI networking model. So they are called level 2 switches. This is the data link layer which pretty much tells you what they are used for. You can now buy switches that feature some routing capabilities which are level 3. These are hyrbid devices that contain the functionality of both types of devices.
Network switches have a lot of features these days. You can choose based on speeds which are copper or fiber. There is the option of layer 2 or layer 3 switches depending on your network's needs. Sizes range from 4 to 48 port usually so there is a lot to choose from there. Extra features you should look at are PoE, IPv6, and redundant power supplies.
Network Router
The most basic function of a router is deciding how and where to send packets of information. It routes information. By routing information a router also connects networks together.
The most common example of this is connecting a Lan with an ISP in order to get outside connectivity to that network and thus get internet access to your Lan. A router is a layer 3 device on the OSI model. This is the networking layer.
It is best to use a hardware router instead of software. This is because physical networking devices will have their own processor and memory so performance will be better.
Network routers also do everything that hubs and switches can do also. This is also why they are generally the most expensive of devices.
Networking routers can also include other great features. A firewall is a very common feature and is a good idea. It will help keep your network safe and working better. Routers will also include VPN's.
This allows offsite connection to your network for those that need it. It is common for businesses to offer this feature to employees. You can control who uses a VPN and what access they have with it. It is quite useful.
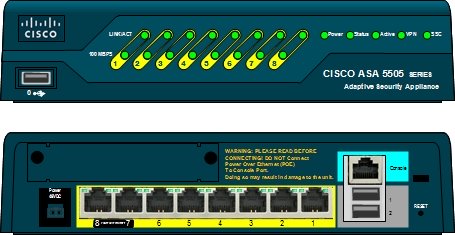
Network Firewall
A firewall is a hardware or software device that provides security by filtering incoming and outgoing network traffic. The traffic is filtered by a set of rules. These rules can be the default as set by the manufacturer or customized by you in software that acts as a firewall. There are a few different types of firewalls too. They are packet filtering, stateful, and application firewalls for your network.
Packet filtering firewalls just examine the network packets themselves. They are not very complicated because of this. They do not consider connections as they are unaware of this factor.
Stateful firewalls can see the connection status of packets. This feature makes them much more valuable and flexible for your system. Only after they have analyzed the packets will they then apply firewall rules to them.
Application firewalls do all of this and more. They actually analyze the data that is transmitted. This is key to maintaining the integrity of your network. This data traffic can then be matched to known sources of either good or bad data set up in your rules.
VPN Concentrator
VPN stand for virtual private network. It is a useful way for people to remotely connect to networks that are in another geographic location. They are often physical network devices. Though similar to a router, it is only for setting up and maintaining VPN's. It will take care of the data and security invovled in users creating their connections. So it sets up VPN tunnels securely and manages all of that for you.
Now a long time ago these VPN concentrators were produced seperately. They were their own physical devices. However, these days the functionality is usually built in to firewalls.
A VPN concentrator, to be clear, is designed for multiple connections occurring from different locations.
A site to site VPN is not the same as a VPN concentrator. It is used for establishing a persistent connection from 1 or 2 locations that never change. An example of this would be two or three offices who want a permanent connection between themselves.
Intrusion Prevention System
IPS stands for Intrusion Prevention System. An intrusion is when someone tries to break into your network. Intruders are often outside your network but unfortunately can also be within your own network. It is always a good idea to watch for this scenario. Its job is to analyze packets and deny them entry if they seem suspicious.
Once an attack has been verified it will then try to log the activity. This is important so the activity can be looked at in detail at a later time. Your IPS will then try to stop the attack. Lastly it will report the attack based on settings you had previously provided.
An IPS can be separate as in software based or it can be part of some firewalls. If you can, it is a good idea to have both a firewall and an IPS. A popular software based IPS is Snort. It is a good idea to have both on your network because it is an extra layer of defense and works differently than firewalls. This difference is what lets them work well together.
This difference is that a firewall either accepts or blocks traffic depending on the rules you provide. An IPS will examine the traffic once it is inside the network and watches it carefully to make sure it does nothing wrong. If the traffic turns out to be bad then it gets blocked.
How IPS Works
It operates between your network and the internet usually. The most common configuration is to sit directly behind the firewall. It is usually a good first buy for companies because it is better to keep intruders and known sources of evil out of your network as a first step.
After you buy one it is important to adjust it to your network needs. If you do not then you will most likely have a large amount of false positives or you will be letting in all kinds of bad traffic. Detection methods are usually signature based. This is the easiest way to block known varieties of attacks instead of just one individual attack at a time.
Ideally after it is set up you would want a few false positives but not too many. This is far better then false negatives into your system. If it is tuned in this way it should keep the attacks out while only giving you a few false positives. That is the goal in setting this system up.
Wired and Wireless Access Points
An access point acts as a distribution center to connect wireless network devices. They can be either wired or wireless themselves. Wired access points are connected by cat5 or cat6 cables if they are wired. Once data reaches an access point it will convert this data to either 2.4 or 5 Gig Hz signals.
Another use is to even connect networks to each other but this is not very common. Even more rarely is to bridge wireless and wired connections. They are usually not smart or managed devices. Essentially they are distribution points. They can connect using wireless signals too.
Since they are distribution points it is important to remember that they do not have any security features like a firewall would. If you have need of those features just make sure you shop around enough to find what you need.
Home Use For Access Points
At home it is often convenient to use wireless versions of these access points in order to give you greater coverage. They are easy to install and just connect wirelessly to your existing router. Businesses will often add several of these a larger building.
If your access point is wired then it is operating in full-duplex mode. This means that it can upload and download data simultaneously. Working this way indicates that your connection is faster and more reliable than wireless. It is more reliable because it can detect collisions of packets.
Now if your access point is wireless it is going to be operating in half-duplex mode. This is essentially half of the connection speed of a wired connection. Also there is no collision detection capability in half-duplex mode.
Network Content Filter
Content filtering is the use of certain kinds of software to screen for objectionable content. This is usually in the form of web pages or email. For web pages it is called web filtering. When dealing with email it is often called anti-spam software.
Web filtering is pretty straightforward. When the data for a web site comes in then the web filtering software examines it and decides if it should be displayed or not. The settings are applied at the router level. From the router all computers that send packets to and from it operate under the settings of the web filtering software.
A good example of web filtering software is OpenDNS. This software is what I use at home. It is free for home use and works very well. It is a very useful network device
Email filtering is similar to web filtering. Your software will examine the incoming email for certain strings of text that identify it as something bad for your environment. This process often works by using rules that you can set up.
There are open source varieties of content filtering as well. These are primarily for Linux/BSD systems. Some of the more popular ones are Untangle and Squid. These allow you to adjust literally every setting. Considering that, they are for more advanced users who want total control over their environment. They do work well though. Any professional IT person would have no trouble with these.
Network Load Balancers
A Load Balancer does one important thing. It distributes network traffic from one source to several sources to lighten the load on any particular server. For large websites this is one of the most important network devices that they will have. This is very important among huge workloads and high traffic servers.
Another example of this a high traffic server that runs a popular application. This technique will increase reliability and performance. Clustered servers or standalone servers will work with a Load Balancer.
The Load Balancer sits between the servers and your internet connection. It handles network traffic from there. If any particular server becomes unavailable the Load Balancer will distribute traffic to the other servers seamlessly. In the same vein, if more resources are added, such as another server, then traffic will automatically get routed to the new server on an equal basis.
This also makes your infrastructure more flexible because you can add or take away servers at any time. The Load Balancer will then re-distribute the network traffic.
Types Of Load Balancers
There are different kinds of Load Balancers. They operate differently based on the needs of your network. Load Balancer Algorithms work in a variety of ways.
- Round Robin - This Algorithm distributes network requests in the order they came.
- Least Connection - This Algorithm looks at the traffic of each server and send its request to the one with the least traffic.
- IP - You can decide where certain IP addresses go from the very start if that is how you want to do it.
They can come in hardware and software versions. There are advantages to each type. Using them helps your reliability too because then you do not have a single pint of failure for your system. This is very important and wise to set up your infrastructure like this.
Hardware Load Balancers will typically work better as long as you have the correct solution in place and have provided for future growth. It has its own processors. They are not very flexible though. For example, if you outgrow your current piece of hardware then you have to buy another usually.
Software Load Balancers are very flexible. Load Balancers can be run on a local server or a virtual server in the cloud. They are most often quite a bit cheaper than a dedicated hardware version. However, they are actually installed on the servers and will use the servers processor and memory to operate.
Conclusion
Any network and its associated network devices will have various and specific needs. No network will have the same needs either outside of basic routing, expansion, and security. Otherwise, they will all be a little bit different. Almost all Lans include these network devices.
There are not many of them but every one of them can contain a myriad of features that would make one a great choice for your network or the wrong choice. So it is vitally important that you decide what your network needs before buying anything.
It was my goal here to clear up some of the differences between devices and help those who might be in the buying stage to make the right choice. Some of these devices are very expensive so making the wrong choice is a bad idea.
If you truly enjoyed reading this article that I wrote then I would ask you to subscribe to my mailing list and share it on your Facebook, Twitter, Google+, or whatever you use. It will help me and my site grow. I would greatly appreciate it.
If you have any comments or suggestions for other tips regarding networking devices then I would love to hear them on the comment section below.